- Who is behind Portapps?
- How to be notified of new releases?
- How to trust your distributed binaries?
- How does it work?
- Antivirus complains about the wrapper
Who is behind Portapps?
Hi, I’m CrazyMax. This project is self-funded and developed using my experience in creating open source software.
By supporting me, you’re not only sustaining this project, but rather all of my open source projects.
How to be notified of new releases?
GitHub is the best way to receive notifications when a new version is released for your favorite application. First of all, have an account on GitHub, then go to the application repository by clicking on the GitHub logo on the app page and then click on Watch ![]() new releases on the repository. Here is an example for Firefox:
new releases on the repository. Here is an example for Firefox:
Go to Postman portable page and click on GitHub logo to access to the repository:
On GitHub choose Watch then Custom and select Releases:
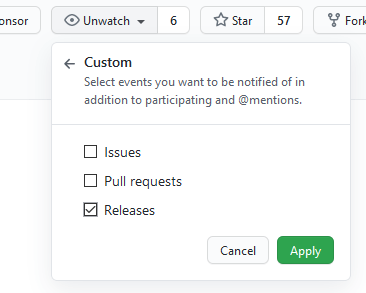
You can also Star ![]() the repository to show your support
the repository to show your support ![]()
How to trust your distributed binaries?
In a word, you can trust portapps binaries over those provided by other systems offering portable applications.
Why? Because the whole process is open source as well as the build process for the executable wrapper. Let’s take Skype as an example.
The “main” file of each portapp repository is the build.properties file. It’s a spec file for the building procedure of a portapp using Apache Ant.
In this file you have the original source of the distributed package from the official website. For Skype this file is at the following url: https://endpoint920510.azureedge.net/s4l/s4l/download/win/Skype-8.25.0.5.exe.
If you go on the official website of Skype the link to the artifact is https://go.skype.com/windows.desktop.download, but it redirects to an azure CDN:
> https://go.skype.com/windows.desktop.download
HTTP/1.1 301 Moved Permanently
> https://get.skype.com/go/getskype-skypeforwindows
HTTP/1.1 302 Found
> https://endpoint920510.azureedge.net/s4l/s4l/download/win/Skype-8.25.0.5.exe
How does it work?
To explain the building process to make it “portapp”, we are going to take Postman as an example.
Everything is revealed in the Actions tab of Postman portable repository. Here are the building steps involved in the Build workflow:
- Checkout repo
- Install Go
- Checkout portapps core repository
- Load required libraries
- ant-contrib
- 7zip
- rcedit (to add icons to the final executable)
- innoextract (to extract the original setup)
- innosetup (to package the final portapp as a portable setup using innosetup)
- upx (to compress the portapp executable)
- hashmyfiles (to create checksums)
- Download the original setup from the official website
- Extract this setup
- Download go modules based on
go.modfile - Go generate (prepare versioning file for the final executable and rcedit resources)
- Go build (create the portapp executable)
- Load asar (tool to extract
app.asar; because Postman is based on Electron) - Replace paths in
app.asar - Repackaging app.asar
- Create 7z portapp archive
- Create innosetup portapp setup
- Send artifacts to Github releases
- Done

This process is quite the same for the current portapps available but can differ following the original setup (can be archive, electron app, innosetup, etc…).
Antivirus complains about the wrapper
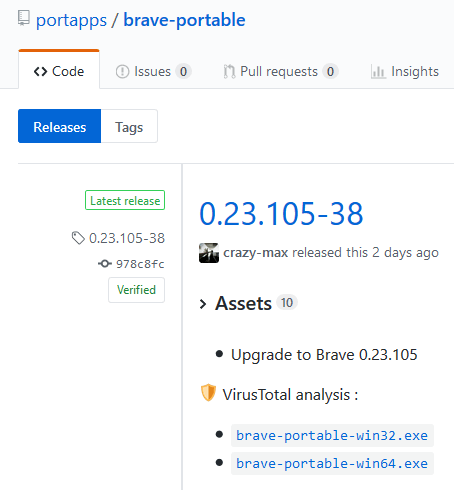
Wrapper [appname]-portable.exe of all portapps are scanned by VirusTotal and a link is provided in the description of GitHub releases page.
Checkout brave-portable releases page on GitHub as an example:
Every detections found by VirusTotal scans are generic. Most likely based on a heuristic detection. Heuristics are more prone to false-positive detections:
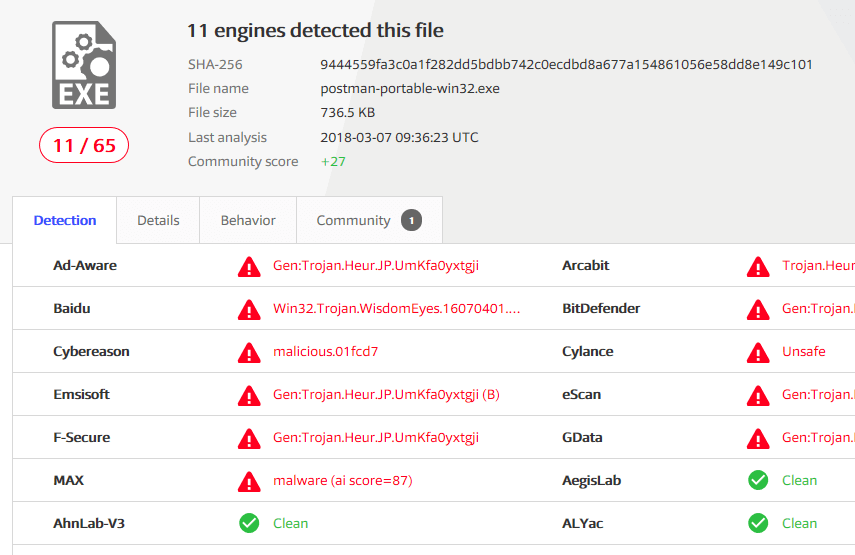
This happens quite often with programs written in Golang. The best you can do is to report this to your Antivirus software vendor as a false positive:
- Adaware: https://www.adaware.com/report-false-positives
- Avast: https://www.avast.com/false-positive-file-form.php
- AVG: https://www.avg.com/en-us/false-positive-file-form
- Bitdefender: https://www.bitdefender.com/submit/
- F-Secure: https://www.f-secure.com/en/web/labs_global/submit-a-sample
- Kaspersky: https://virusdesk.kaspersky.com/
- McAfee: https://kc.mcafee.com/corporate/index?page=content&id=KB85567
- Windows Defender: https://www.microsoft.com/en-us/wdsi/filesubmission
And this is often quickly solved: portapps/skype-portable#4, portapps/postman-portable#1